
- Bitdefender identified a new attack attributed to a sophisticated actor offering advanced-persistent-threats-as-a-service
- The targeted company is engaged in architectural projects with billion-dollar luxury real-estate developers in New York, London, Australia and Oman
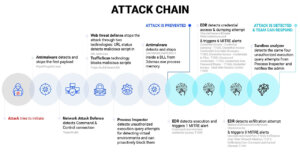
- The Bitdefender technology stacks detect the used payloads as well as the malicious behavior
Bitdefender researchers recently uncovered a sophisticated APT-style attack targeting an international architectural and video production company. The attack shows signs of industrial espionage, similar to another of Bitdefender’s recent investigations of the StrongPity APT group. The real-estate industry is highly competitive, and information exfiltrated by APT mercenary group can give negotiation advantages to other players in high-profile real-estate contracts.
While APT groups traditionally could only be afforded by governments or were financially motivated purely out of self-interest, they recently appear to have become a commodity. While full technical details of the investigation are available in a detailed paper on Bitdefender Labs, here we’ll focus on how and what tools companies of all sizes and across all verticals can have at their disposal to identify these new and sophisticated attacks.
In the following, we’ll focus on which technologies from a security stack can actually detect such a sophisticated attack during various steps in the attack chain, and also focus on how the MITRE attack tactics and techniques framework that’s part of your EDR solution can help give early warning signs of a potential breach, and how to plug it.
The anatomy of today’s industrial cyber-espionage
APT-as-a-service is becoming a reality, with highly skilled cybercriminal groups offering their services to companies willing to spare the cash necessary to contract their skills. While traditional cyber-espionage was reserved to state-sponsored benefactors, it seems that industrial espionage for companies with deep pockets could become a mainstream tool to spy on competition.
A recent Bitdefender investigation revealed that APT mercenaries could be used by luxury real estate investors involved in multi-billion-dollar contracts to spy on competition or contractors involved in massive development projects. The goal probably involves gaining inside knowledge about negotiations, prices and contracts so that whoever contracted the APT-level hackers gain a negotiation advantage.
In this case, the targeted company is engaged in architectural projects with billion-dollar luxury real-estate developers in New York, London, Australia and Oman. With offices in London, New York and Australia, the company’s customers and projects involve luxury residences, high-profile architects and world-renowned A-list interior designers.
During the investigation, Bitdefender researchers also found that threat actors had an entire toolset in place, featuring powerful spying capabilities. Based on Bitdefender’s telemetry, we also found similar malware samples communicating with the same command and control server, dating back just under a month ago. Located in South Korea, the US, Japan and South Africa, it’s likely the cybercriminal group has also been targeting select victims in these regions.
MITRE Helps Identify Tactics
For starters, while most companies, regardless of size, have implemented basic endpoint security technologies to protect against garden-variety malware, these sophisticated threats can fly below the radar and completely dodge, at least for a while, these solutions.
The traditional security stack mostly involves file-based detection technologies, which can sometimes miss sophisticated threats for obvious reasons, such as polymorphic malware samples, fileless malware or even legitimate living-off-the-land tools such as RDP services that can be abused by threat actors. Consequently, MITRE has created a knowledge base of adversary tactics and techniques based on real-world observations that can help organizations identify signs of a potential data breach that would otherwise be missed by the traditional security stack.
For instance, while security solutions focus on identifying malicious payloads or URLs, MITRE’s framework focuses on identifying behavior such as uncommon ports in use, command line interfaces being triggered, and even suspicious copy-paste activities triggered by automated scripts. While these are not malicious actions per se, they can indicate suspicious behavior usually associated with advanced threat actors performing various actions.
During Bitdefender’s investigation into this particular APT-style attack, our EDR (Endpoint Detection and response) technology flagged several MITRE techniques employed during the attack:
- T1011 – Exfiltration Over Other Network Medium
- T1041 – Exfiltration Over Command and Control Channel
- T1059 – Command-Line Interface
- T1065 – Uncommonly Used Port (as part of the “Command and Control” category)
- T1539 – Steal Web Session Cookie
- T1081 – Credentials in Files
- T1003 – Credential Dumping
- T1503 – Credentials from Web Browsers
- T1552 – Unsecured Credentials
- T1555 – Credentials from Password Stores
There was also an EDR alert called MalwareExfiltrationOverNetwork that was triggered by our EDR solution. All these alerts potentially signal to an IT or security team that a security incident could be in progress.
Relying on these MITRE ATT&CK® alerts can help organizations investigate potential signs of intrusions and find out where are their security blind spots and address them. For instance, knowing what ports their applications commonly use when communicating over the internet can help them restrict access on any unused ports, effectively blocking any threat from communicating with a Command & Control server. At the same time, understanding that hidden command-line interfaces are often used by attackers to automate various tasks, IT and security teams can set up policies restricting these from executing on endpoints.
Bitdefender Technology Stack Detects Behavior and Payloads
While the MITRE framework is powerful when it comes to spotting anomalous behavior, the security stack should not be underestimated. For example, when facing the Bitdefender security stack, the investigated APT-style attack can be spotted and successfully blocked by several Bitdefender security technologies during multiple steps in the attack chain.

Bitdefender anti-malware technology successfully detects malicious payloads with the following detections: Gen:Variant.Rudid.Bulz.*, Trojan.Agent.EUWF, Trojan.MSIL.Rudid.*, Trojan.Rudid.GenericKD..
Bitdefender HyperDetect technology, which uses highly tuned machine learning models for spotting new and unknown malware with 99.99% accuracy, also detects some of the malicious payloads used with the following detections: Illusion.ML.Miura.*, Illusion.ML.Skyline.9.*, Illusion.ML.Skyline.B.*.
Bitdefender Theta technology, which is 100% machine learning-powered and uses deep neural networks and state-of-the art cloud-based dynamic behavioral analysis, also detects some of the malicious payloads with a specific model: Gen:NN.ZemsilF.34152.qiZ@a4Dx@1m and Gen:NN.ZemsilCO.34152.qiZ@a4Dx@1m.
Bitdefender URL-Status technology, used for identifying malicious, fraudulent or otherwise suspicious links, also blocks malware’s attempts to contact the Command & Control server, potentially plugging the attacker’s ability to remotely control the threat by giving it further instructions or blocking it from exfiltrating data.
Bitdefender ATC (Advanced Threat Control) and Sandbox are two dynamic detection technologies that can detect the threat, even though the malware pack features are designed to identify if it’s running in a protected environment.
Bitdefender Network Attack Defense, a technology focused on detecting network attack techniques designed to gain access to endpoints also specific malicious payload Trojan.Rudid.
Fighting APTs is a Marriage of Two Paradigms
Having a full endpoint security stack that can identify malicious behavior and payloads in various steps of the attack chain is vital in detecting these types of commoditized APT-style attacks. However, when the security stack falls short of revealing the full intent and scale of an attack, turning to an EDR solution that applies MITRE advanced tactics and techniques in identifying security incidents is the next step towards both understanding and blocking where the attack originated and how far in the attack chain attackers managed to reach.
Considering the ever-evolving nature of the threat landscape and that APT mercenaries offering their skills as a service will continue to target companies of all sizes and across all verticals, it’s now becoming mandatory to turn to capable and easily manageable EDR solutions that can flag suspicious events that the security stack might otherwise dismiss.