
Managed Detection and Response (MDR) Insights
Let’s talk about credential leaks. Whether it’s a new breach or a recycled list, credential leaks remain a valid threat to organizations. Credentials, which are user emails and corresponding passwords for a given site or application, are a cybercriminal’s favorite data type because they allow them to masquerade as a legitimate user on a system. Since January, 62% of Bitdefender’s MDR’s actionable intelligence alerts have been credential leaks. As we have seen within the last 2+ years, these attack vectors are industry and location agnostic, and they’re only increasing. Verizon’s Data Breach Investigations Report indicates that credentials made up 42% of all data compromised by APTs in 2021, stating, “if you can access the asset directly over the internet simply by entering the credentials, so can the criminals”.
Credentials are sold and distributed on dark web sources and can be found in code repository pages that are easily accessible to anyone. But are you still at risk even if your company requires users to follow best practices, including password complexity, length, and a quarterly change? The answer is potentially. With many organizations using hybrid and remote working models, personal devices are a blind spot. The MDR Intelligence Cell has access to sources called Malware Logs which give insight into spyware devices. Spyware can affect personal computers as well as Apple and Android mobile devices. Attackers usually try to catch unsuspecting users logging into important financial or work resources, and personal devices may not have up-to-date security tools. Spyware steals login information and releases it on dark web markets within 30 days, which could mean they have current credentials.
There are several ways that attackers use compromised credentials. They may use combinations of usernames, emails, and exposed passwords to gain initial access through web portals or other remote accesses like RDP, VPN, or SSH through brute-forcing or credential stuffing attacks. Spammers and other social engineering attacks, such as phishing and spearphishing, might also use emails to attack corporate or personal emails that are likely active.;
When it comes to credential leaks, some security measures that can be taken include the following:
-
Apply Multi-factor authentication;
-
Awareness: Detection/crawling of dark web, closed sources, and paste sites to find leaked business credentials such as conducted by a cyber intelligence service included in Bitdefender MDR.
-
Business email addresses should only be used on business accounts.
-
Apply strong security practices when it comes to passwords.
-
Use a Password Manager
-
The password length is very important. Be sure to have 12-14 characters.
-
Including upper- and lower-case letters, numbers, and symbols adds complexity.
-
Length is more important than complexity, and points 6 & 7 combined make passwords even harder to crack.
-
For example, you can select a few random words, exchanging numbers and symbols for letters: Halloween Shoes Car becomes H@l10w3en$4oe&c@R.
-
Do not use the same password(s) across multiple accounts.
-
Update/change passwords at least every 90 days.
-
Whenever possible, enable password-less authentication, like OIDC (OpenID Connect), within your organization tools, and make sure third-party software and platform vendors are compatible with those standards in order to apply single-sign-on authentication.
-
Implement IP/URL reputation for endpoints to block access to credential-stealing sites.
Ransomware Report
Spear phishing attacks are often used as an initial attack vector and ransomware infection is often the final stage of the kill chain. For this report, we analyzed malware detections collected in June 2022 from our static anti-malware engines. Note: we only count total cases, not how monetarily significant the impact of infection is. Opportunistic adversaries and some Ransomware-as-a-Service (RaaS) groups represent a higher percentage compared to groups that are more selective about their targets, since they prefer volume over higher value.
When looking at this data, remember these are ransomware detections, not infections.
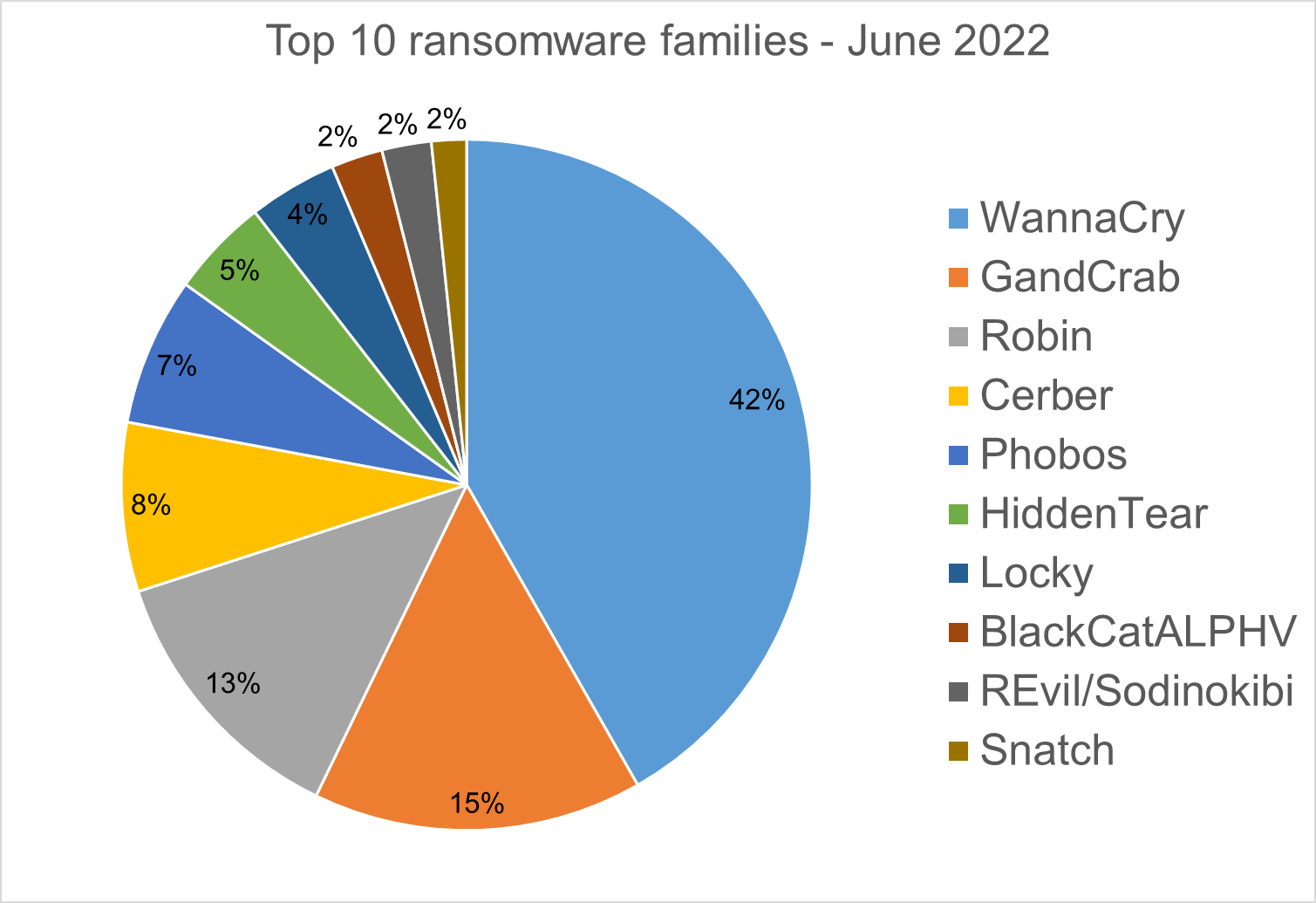
Top 10 Ransomware Families
We analyzed malware detections from June 1 to June 30. In total, we identified 192 active ransomware families. Number of detected ransomware families can vary each month, depending on the current ransomware campaigns in different countries.
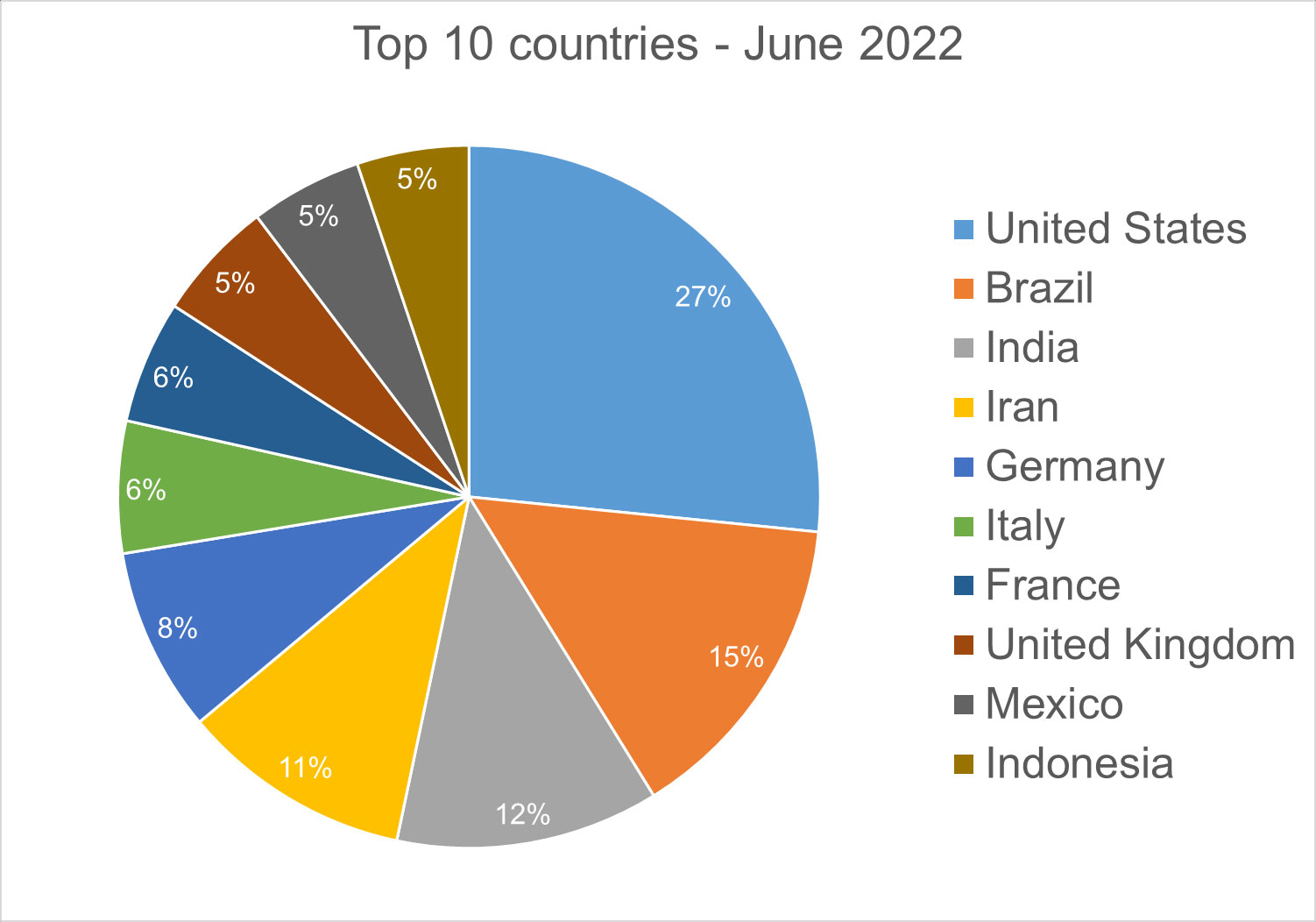
Top 10 Countries
In total, we detected ransomware from 156 countries in our dataset this month. Ransomware continues to be a threat that touches almost the entire world. Below is a list of the top 10 countries most impacted by ransomware. Many ransomware attacks continue to be opportunistic, and the size of population is correlated to the number of detections.
Android trojans
Below are the top 10 trojans targeting Android we have seen in our telemetry during June 2022.
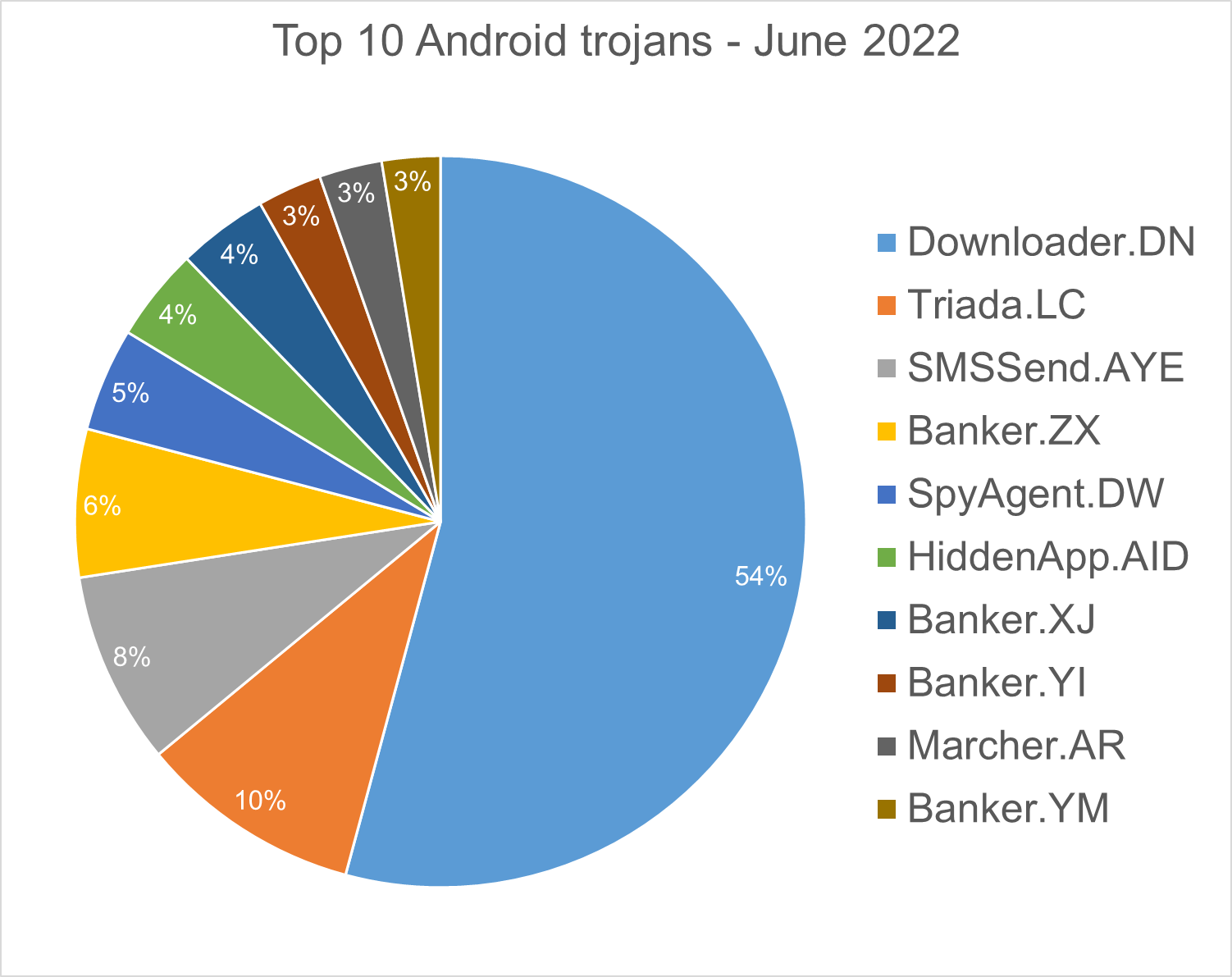
Downloader.DN – Repacked applications taken from Google App Store and bundled with aggressive adware. Some adware downloads other malware variants.
Triada.LC – Malware that gathers sensitive information about a device (Device IDs, Subscriber IDs, MAC addresses) and sends them to a malicious C&C server. The C&C server responds by sending back a link to a payload which the malware downloads and executes.
SMSSend.AYE – Malware that tries to register as the default SMS application on the first run by requesting the consent of the user. If successful, it collects the user’s incoming and outgoing messages and forwards them to a Command & Control (C&C) server.
Banker.ZX – Applications that disguise themselves as banking apps and can imitate conversation with customer support. When the malware runs for the first time, it asks for permissions to access contacts, microphone, geolocation, and camera. Once the permissions are granted, the malware can receive commands from the C&C server to exfiltrate sensitive data from the phone.
SpyAgent.DW – Applications that exfiltrate sensitive data like SMS messages, call logs, contacts, or GPS location.
HiddenApp.AID – Aggressive adware that impersonates AdBlock applications. When running for the first time, it asks permission to display on top of other apps. With this permission, the application can hide from the launcher.
Banker.XJ, YM – Applications that drop and install encrypted modules. This trojan grants device admin privileges, and gains access to manage phone calls and text messages. After deploying, it maintains a connection with the C&C server to receive commands and upload sensitive information.
Banker.YI – Polymorphic applications that impersonate legit apps (Google, Facebook, Sagawa Express …). Once installed, it locates banking applications installed on the device and tries to download a trojanized version from the C&C server.
Marcher.AR –Applications that disguise themselves as Play Store applications. The malware tries to ask for accessibility permissions to capture keystrokes and uses the VNC screen recording function to log user’s activity on the phone.
Homograph Phishing Report
Homograph attacks work to abuse international domain names (IDN). Threat actors create international domain names that spoof a target domain name. When we talk about “target” of IDN homograph phishing attacks, we refer to the domain that threat actors are trying to impersonate. You can read more about this type of attack in one of our previous reports.
Below is the list of the top 10 most common targets for phishing sites.

About Bitdefender Threat Debrief
The Bitdefender Threat Debrief (BDTD) is a monthly series analyzing threat news, trends, and research from the previous month. Don’t miss the next BDTD release, subscribe to the Business Insights blog, and follow us on Twitter. You can find all previous debriefs here.
Bitdefender provides cybersecurity solutions and advanced threat protection to hundreds of millions of endpoints worldwide. More than 150 technology brands have licensed and added Bitdefender technology to their product or service offerings. This vast OEM ecosystem complements telemetry data already collected from our business and consumer solutions. To give you some idea of the scale, Bitdefender Labs discover 400+ new threats each minute and validate 30 billion threat queries daily. This gives us one of the industry’s most extensive real-time views of the evolving threat landscape.
Wewould like to thank bitdefenders Tyler Baker, Alin Damian, Mihai Leonte, Andrei Mogage, Sean Nikkel, Nikki Salas, Rares Radu, Ioan Stan, Marius Tivadar, and Horia Zegheru (sorted alphabetically) for their help with putting this report together.