Browser-in-the-browser (BitB) attacks are now possible, according to a security researcher who devised a new way to trick people into thinking they are accessing genuine authentication windows.
When people hear about phishing, they imagine annoying emails that are usually easy to recognize. But there’s a second part of the phishing problem, that of the websites where criminals redirect their victims. Fake websites trick users into thinking they are in the right place. Most astute users look at the URL in the browser and notice that it’s not the correct one, immediately raising suspicions.
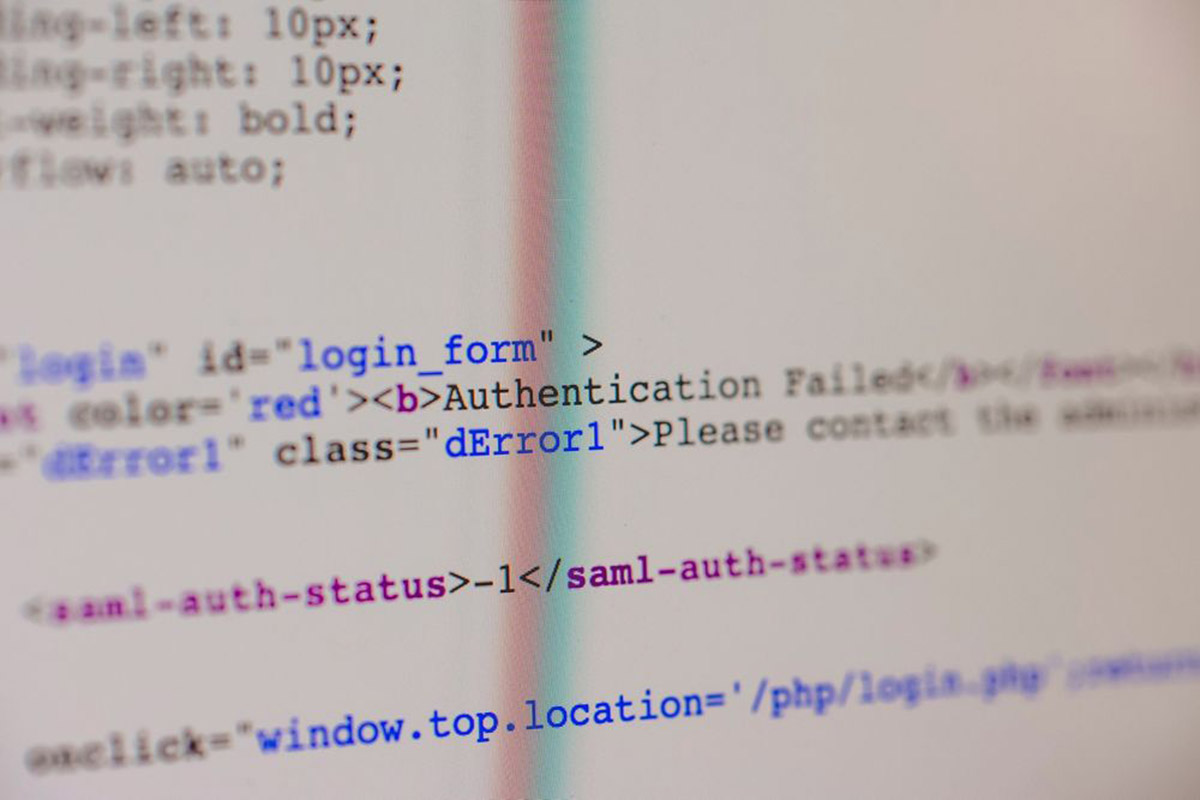
A security researcher going by the moniker of mr.d0x figured out a way to hijack the pop-up windows we usually get when using other services to authenticate, such as Google or Facebook.
“Combine the window design with an iframe pointing to the malicious server hosting the phishing page, and it’s basically indistinguishabl0,” said the researcher. “Very few people would notice the slight differences between the two.”
“JavaScript can be easily used to make the window appear on a link or button click, on the page loading etc. And of course you can make the window appear in a visually appealing manner through animations available in libraries such as JQuery,” he added.
His demonstration goes even further, as he managed to find a way to show a custom URL when a mouse hovers on it, strengthening the illusion of legitimacy. The scenario is simple: the victim clicks on a phishing link and gets redirected to a fake website that presents a fake authentication window with all the signs of a legitimate URL.
Phishing and the entire infrastructure are evolving alongside all the other threats. It’s becoming more difficult to identify fake websites and phishing attempts visually, so a security solution that prevents users from accessing the fake URLs in the first place becomes mandatory. Bitdefender’s Total Security offers the right tools needed to stay safe online, and it covers this kind of scenario as well.