
A new phishing campaign leveraging bogus bonus payments from the HR department is targeting employees and remote workers across the globe to steal business login credentials.
This phishing attempt, caught by Bitdefender Antispam Lab earlier this week, originates from IP addresses in Russia and has spread organically to inboxes in the US, UK, Ireland, Sweden, Denmark, Sweden and Romania.
HR-related topics have become an attractive go-to recipe for successful account takeover attempts and business compromise since the beginning of the pandemic.
While previous attacks leverage internal policy changes or notifications alerting employees about password checks and security-related notifications, the ongoing campaign uses a different tactic.
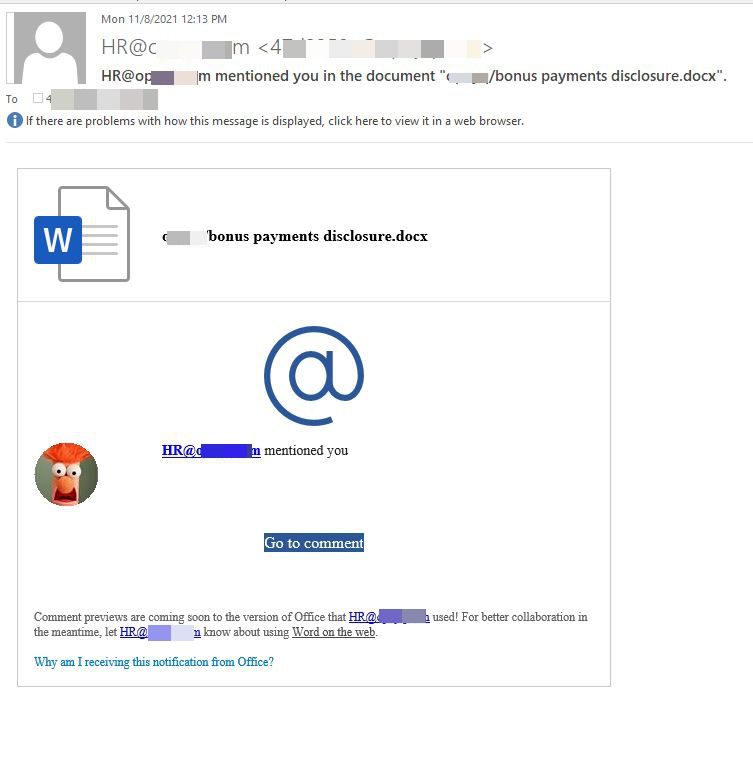
Recipients are lulled into accessing a bogus word document allegedly containing information on bonus payments. It may seem like the attackers put little effort into gift-wrapping the fake email, but what better way to pique an employee’s interest and curiosity, than baiting them with potential monetary bonuses.
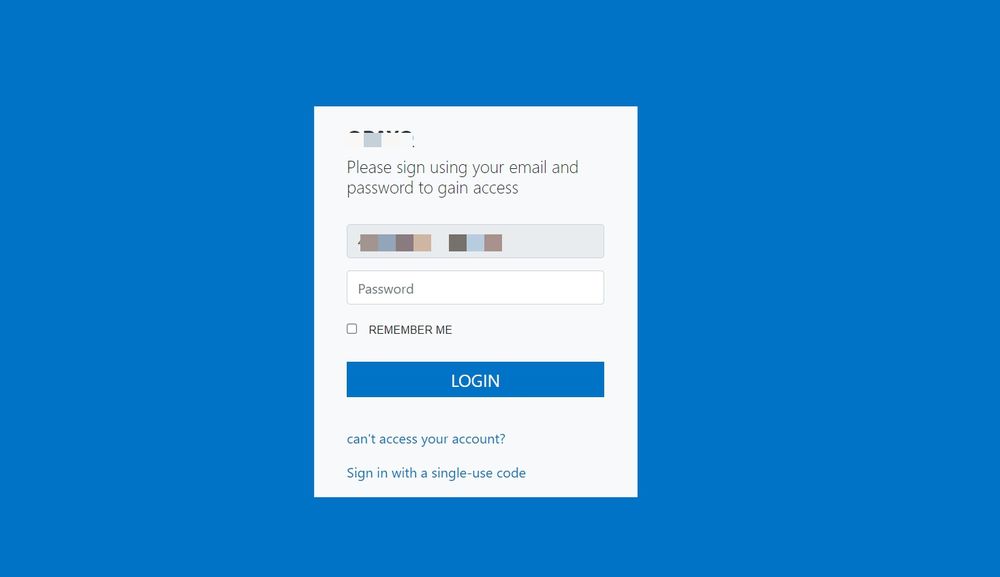
Threat actors have their sights set on businesses and organizations, and often use employee carelessness to compromise internal networks and cripple businesses in targeted ransomware attacks. Credential phishing puts both employers and employees at risk. The hybrid work environment and increased personal use of corporate devices add to the long list of cybersecurity mishaps provoked by employees who fall for malicious correspondence.
Coveted phished employee credentials let attackers bypass an organization’s security measures to steal critical data. Bitdefender recommends employees take extra care when reading emails, even those that apparently come from an employer, HR or IT department.
Users who receive similar emails should immediately send them to their IT department. When in doubt, it’s best to ask for assistance or details from your human resource department before accessing any links, downloading attachments, or entering your corporate login credentials onto an online form.
Note: This article is based on technical information courtesy of Bitdefender Labs
Stay Safe!