
In the last two weeks, a series of phishing campaigns disguised as official banking correspondence targeted Inboxes of Italian customers, according to the Bitdefender Antispam Lab
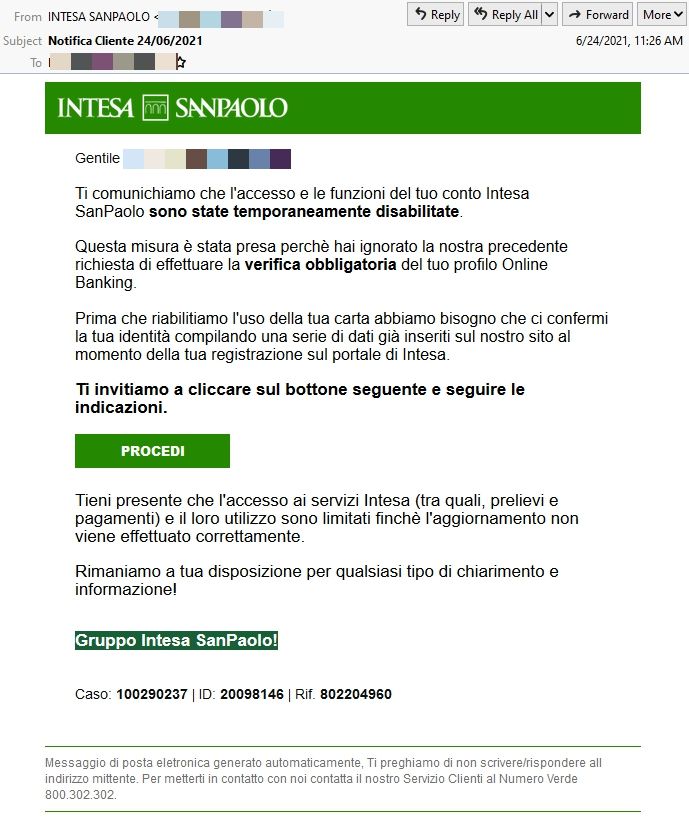
- An Intesa Sanpaolo phishing campaign was active between 23-24 June
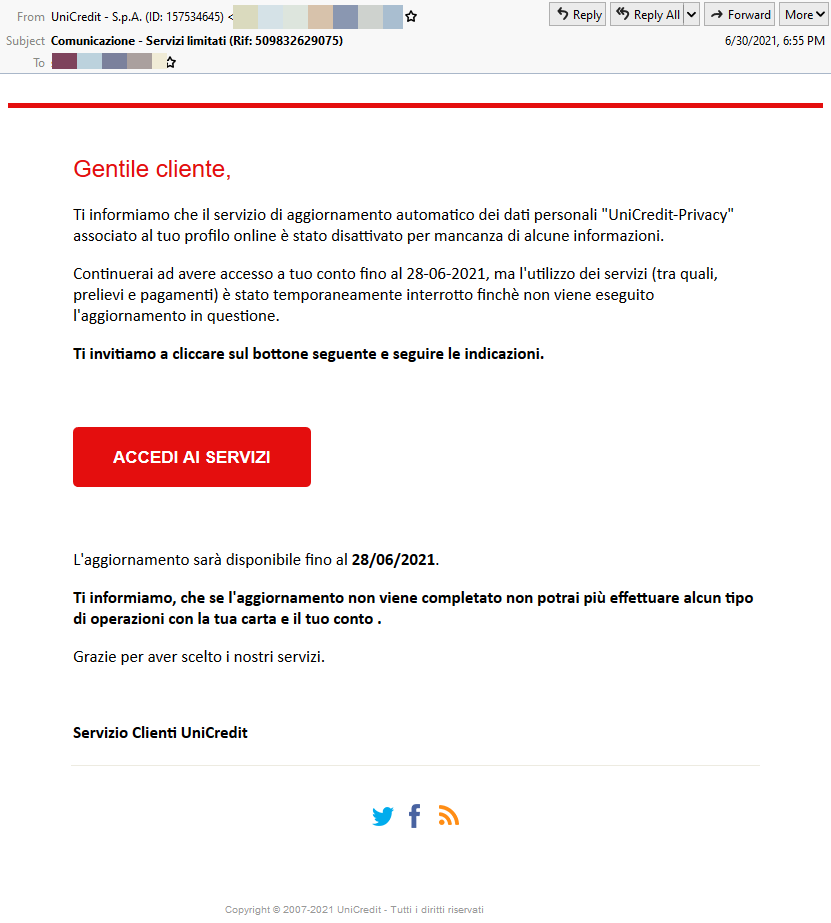
- A UniCredit phishing campaign was active between 28-30 June
The email-based bank impersonation scams were tailored for maximum efficiency, using authentic logos, industry lingo and specific email layouts to resemble legitimate correspondence from the two financial institutions.
The phishing attacks, apparently originating from IP addresses in Japan, are the product of the same gang. The scammers switched between names of popular banks during the campaigns, rolling out a brief two-day phishing attack, undoubtedly to sneak past fraud detection and anti-phishing mechanisms.
The Intesa Sanpaolo scam emails inform recipients that their account has been temporarily suspended, pending a failed request to perform a mandatory verification of their online banking profile. In addition, credit card usage and online banking transactions have been disabled, the scammers warn. To regain access, customers need to confirm their identity by filling out the same data entered during their initial registration process on the Intesa web portal.
The UniCredit scam email is similarly crafted, seeking to panic customers. To reactivate their account and re-enable withdrawals or payments using the bank account, users need to update some personal information.
The cybercriminal operations behind these scams are well-planned and continue to exploit the surge in online transactions and increase mobile banking usage. The actors behind the most recent fraud emails will undoubtedly return with another bank impersonation duo in coming weeks. Future attempts at hijacking login credentials or account information to defraud customers may also arrive via password reset emails or fraud alerts. Either way, these attacks are designed to pressure targets into taking immediate action.
Bad actors often pose as representatives of financial institutions to steal login information or financial data from victims. Users should remain hyper-vigilant and treat any incoming unsolicited emails that ask for personally identifiable information with caution.
When in doubt, call your bank or go to the bank’s official website to verify, without accessing the link in the suspicious email, of course.
Note: This article is based on technical information provided courtesy of Bitdefender Antispam Lab