
Ransomware gang Conti blamed for attack on Florida-based Leon Medical Center Malware delivered via a poisoned document mistakenly opened by staff member The Florida-based Leon Medical Center and Nocona General Hospital in Texas have suffered attacks from hackers that have resulted in extensive information about their patients being published on the internet.
As NBC News reports, “at least tens of thousands” of files containing patients’ names, addresses, birthdays, social security numbers, Medicaid numbers, prescription details, health insurance information, medical diagnoses, and scan results have been posted on the dark web in what is seemingly an attempt to extort money from the organisations.
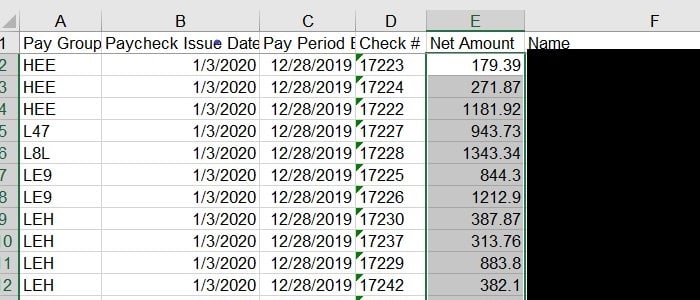
Some of the information is extremely personal, such as an Excel spreadsheet named “2018_colonoscopies” which contains the names of 102 patients, the date and details of their procedures, and an indication of whether they have a “normal colon” or not.

Leon Medical Center, which operates at eight locations in Florida, announced in January that it had discovered in November 2020 that it had fallen victim a malware attack.
The DataBreaches.net blog reported that the attack was the work of the Conti ransomware gang, and that the hackers claimed to have infected the hospital chain’s systems initially by sending an employee a boobytrapped document which exploited a serious remote code execution vulnerability in SMBv3 that Microsoft patched in March 2020.
Unfortunately it appears that hundreds of thousands of former and current patients and employees may be impacted as a consequence of that failure to properly secure systems.
Yolanda Foster, a Leon Medical Center spokesperson, told NBC News that it was working with third-party cybersecurity experts to investigate the breach, and would be directly contacting affected individuals as soon as possible.
Curiously, although Nocona General Hospital has also had sensitive medical details published on the web, the firm is reported by NBC News to have not been hit by ransomware, and that its data was not encrypted following exfiltration.
Brian Jackson, an attorney representing Nocona, also told the media outlet that the healthcare provider had not received a ransom demand:
“I can’t tell you with absolute certainty that they did not send a ransom demand,” he said in a phone call. “I can tell you we did not open one.”
It’s unclear what benefit there is for criminal gangs to publicly dump on the web the sensitive medical information of patients when a ransom is not received, other than to send a message to future victims that their threats are genuine.
At the end of October 2020, the US government issued an updated warning about the threat posed by ransomware against the US healthcare industry, specifically calling out Conti, and its close cousin Ryuk.
Unfortunately that warning does not seem to have been enough to protect some US hospitals from being attacked and their patients and workers being put at risk.