
- TransLink confirms attack saw hackers access staff payroll details
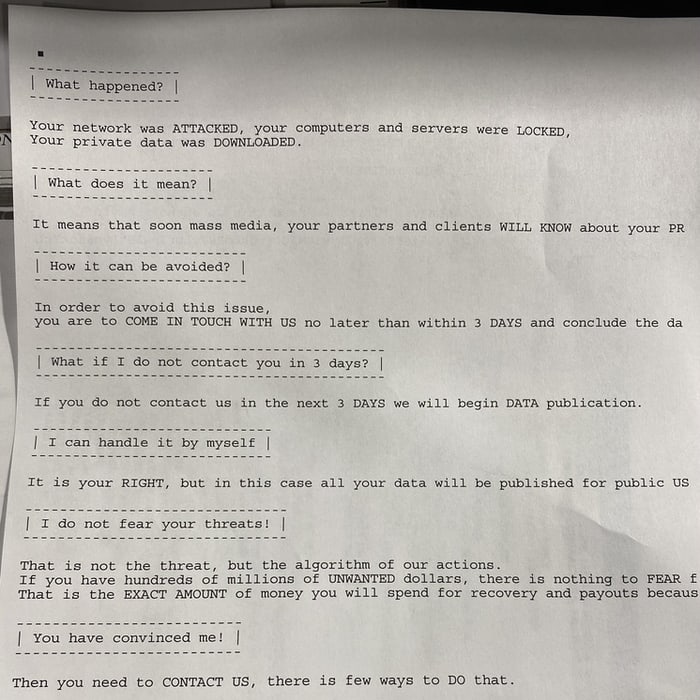
- Egregor ransomware spat ransom demands out of hijacked printers
According to media reports, TransLink, Metro Vancouver’s public transportation agency, has warned its staff that hackers accessed their personal bank account details and other information.
The warning came in an internal email to workers approximately one month after Translink was struck by the Egregor ransomware and passengers had their journeys disrupted.
The email, seen by Global News advised staff that the hackers had “accessed and may have copied files from a restricted network drive” containing payroll information including banking details and social security numbers.
Workers were strongly advised to sign up for two-year credit monitoring at no cost.
The good news for passengers of Translink services is that the company does not store or have access to travellers’ payment information, and so it is only the firm’s employees that have been put at risk by the attack.
The attack, at the beginning of December 2020, saw hackers access company databases, plant the Egregor ransomware which locked down systems by encrypting data files, and even churn out a ransom note on hijacked printers.
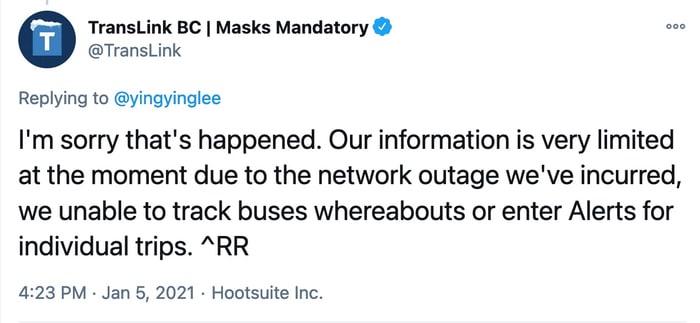
Although passenger data was not apparently exposed, the attack on the TransLink service prevented travellers from being able to use their credit and debit cards for ticket payments.
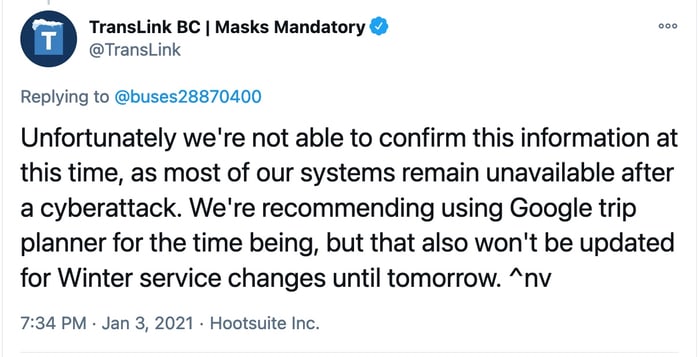
Now, a month since the initial attack, Metro Vancouver’s public transport system has not fully recovered.
In a tweet, the company acknowledged that most of its systems “remain unavailable after cyberattack.”
From the sound of things, TransLink was unwilling to pay a ransom to the extortionists who attacked its systems with the Egregor ransomware. That’s an admirable stance to take, as paying ransoms undoubtedly encourages others to launch similar attacks in the future.
But it also means that, if you do not have a disaster recovery plan in place which can get systems up-and-running again from secure backups in a prompt fashion, that you could be left waiting an awfully long time before normal service is resumed.
Other recent victims of the Egregor ransomware include recruitment giant Randstad, video game maker Ubisoft, and South American retail giant Cencosud.