Security researchers found 134 vulnerabilities in the way apps such as Adobe Acrobat and Microsoft Word handle JavaScript. Experts developed a tool to help them with the task and called it Cooper, in reference to “Cooperative mutation,” a technique employed by the tool.
Of the 134 flaws identified by the app, 59 were considered fit to receive fixes by vendors, 33 received CVE numbers, and 17 yielded a total of $22,000 in bug bounty payments. During the Black Hat Asia conference in Singapore, Chinese Academy of Sciences’ Ph.D. student Xu Peng, a co-author of the tool, said that certain apps, such as Word and Acrobat, allow scripting language input.
Xu elaborated that Adobe Acrobat permits PDF manipulation through JavaScript, which requires the document to define native PDF objects and parse JavaScript code. In this situation, Acrobat modules handle the native PDF objects, while a built-in JavaScript engine handles the scripts, and a “binding layer” translates the information.
The “cooperative mutation” technique the tool uses to identify flaws “simultaneously modifies the script code and the related document objects to explore various code paths of the binding code,” according to Xu.
According to the project’s GitHub page, the tool has three components:
- Object Clustering: Cooper first extracts native objects by parsing sample documents, and categorizes objects into attribute-based classes to reduce object search space
- Relationship Inference: The tool combines different API groups and object classes to produce a large number of documents, then records the execution results of embedded scripts. Cooper then infers the relationship between object classes and API groups based on the success rate of the distribution of object classes and script execution.
- Relationship – Guided Mutation: Finally, the tool guides the script generation, object selection, and object mutation by leveraging the inferred relationship.
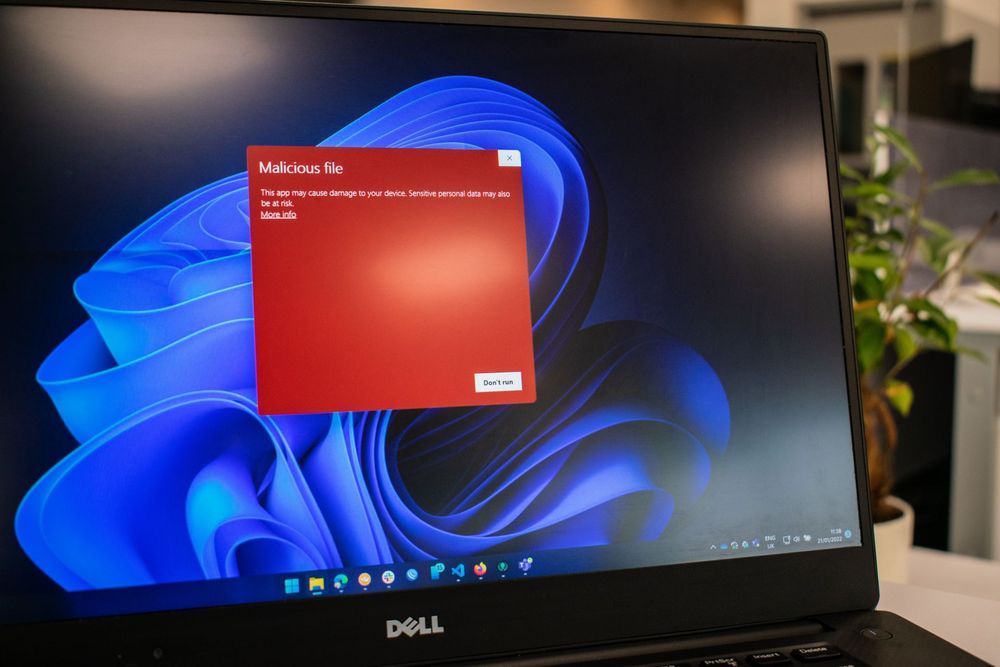
Two of the vulnerabilities Cooper detected, marked as CVE-2021-21028 and CVE-2021-21035, have CVSS severity scores of 8.8 and are both Use After Free Acrobat Reader DC vulnerabilities. These flaws could let an unauthenticated attacker execute arbitrary code remotely. Exploiting these vulnerabilities would require user interaction in that the victim would have to open a malicious file.