
A recent phishing campaign targeting Windows machines is attempting to infect users with one of the most recent versions of the Agent Tesla remote access Trojan (RAT).
The malicious campaign, spotted by the Bitdefender Antispam Lab, tries to deliver the malicious payload under the guise of a COVID-19 vaccination schedule that comes as an attachment.
Most of the attacks seem to have originated from IP addresses in Vietnam. Although telemetry shows a global dispersion of the malspam campaign, 50% of the malicious emails were directed to South Korea.
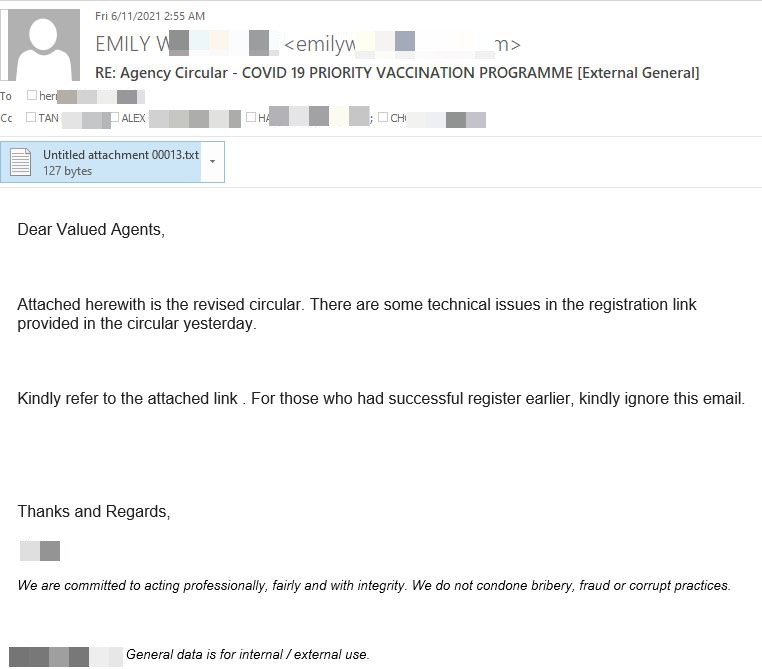
The messages are designed to look like a business email asking the recipients to go over some technical issues presented in the attachment and register for the vaccine.
“Attached herewith is the revised circular,” the malicious email reads. “There are some technical issues in the registration link provided in the circular yesterday. Kindly refer to the attached link. For those who had successful register earlier, kindly ignore this email.”
Active for over seven years, Agent Tesla has been used frequently in phishing campaigns seeking to steal user credentials, passwords and sensitive information.
The updated password-stealing capabilities and security-dodging techniques paired with the malware distribution-as-a-service business model have proven highly profitable.
Agent Tesla’s popularity surged during the second half of 2020, with more than 46% of all global Agent Tesla reports occurring in Q4.
The malicious attachment (AC 2021 09 V1.doc) is in fact a RTF document exploiting a known Microsoft Office vulnerability. Once accessed, the document downloads Agent Tesla malware.
After the malware has collected all the information from the victim’s system, it exfiltrates the credentials and other sensitive data via the SMTP protocol (email) back to an email account registered in advance by the attackers.
According to a joint CISA and FBI advisory, CVE-2017-11882 was among the most exploited software vulnerabilities between 2016 and 2019. So it seems that bad actors are still hunting for outdated and unpatched software that can easily be compromised.
Indicators of compromise
| MD5 | Name |
| 5e7a8b39eff3dfe0374c975fe75a5304dc64b85da4788153796a9bb1f6d44c3c | Trojan.GenericKD.46463520 |
| 675e2470a3c7fe645fe445c95ae152a2dd2d2ccedb366e3cc1e070bb31c59ec4 | Trojan.GenericKD.46464231 |
Bitdefender detects the AC 2021 09 V1.doc as Trojan.GenericKD.46463520, while Agent Tesla malware is detected as Trojan.GenericKD.46464231.
To avoid device and data compromise, always verify the validity of messages before accessing any attachments, patch any used software and install a security solution on your device. With Bitdefender Total Security, you get the best anti-malware protection against e-threats across all major operating systems. The real-time protection feature included in our security software offers continuous protection against all e-threats, including viruses, worms, Trojans, ransomware, zero-day exploits, rootkits and spyware to keep you and your data safe.
Note: This article is based on technical information provided courtesy of Bitdefender Labs