Wordfence Threat Intelligence researchers identified a WPGateway zero-day flaw that has been wielded in recent attacks against WordPress websites running the plugin.
The vulnerability, tracked as CVE-2022-3180, is an unauthenticated privilege escalation flaw that could let attackers add a rogue administrator account to vulnerable websites. Perpetrators could abuse the malicious account’s administrator privileges to take over compromised sites completely.
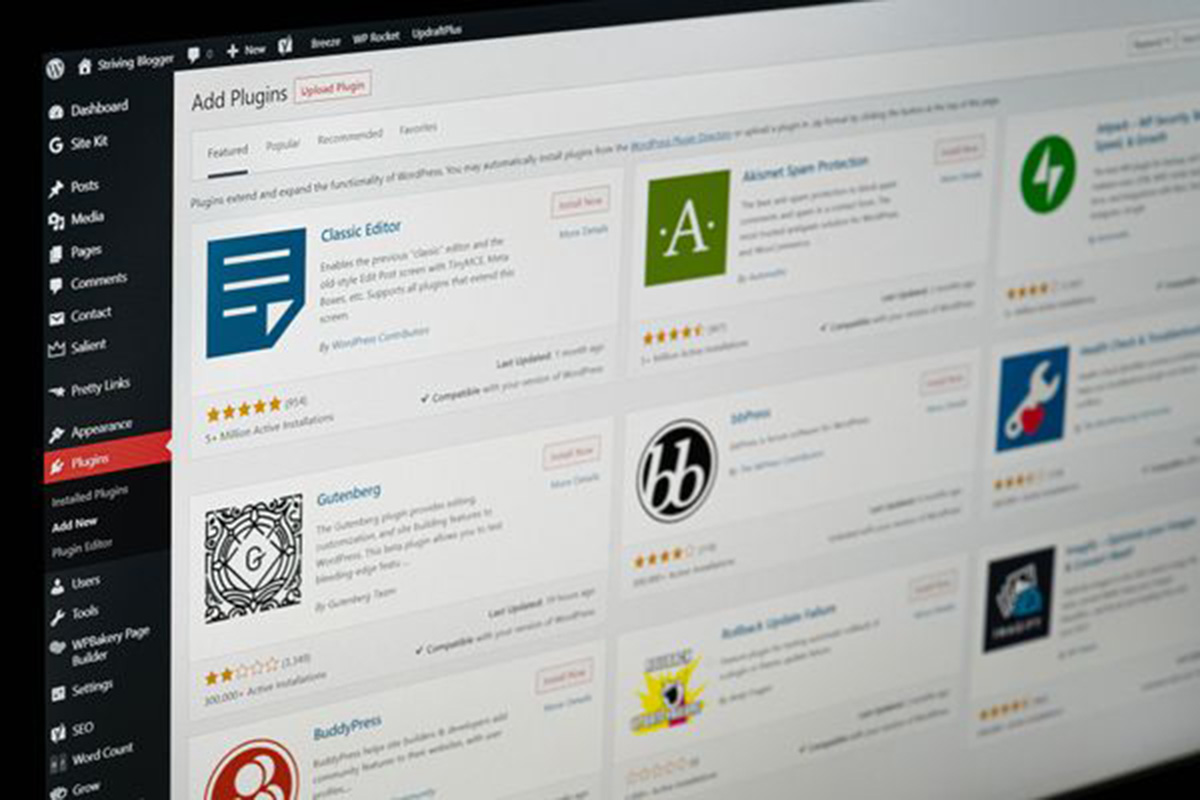
WPGateway is a premium plugin that gives WPGateway cloud users a dashboard to configure and manage WordPress websites. An essential component of the plugin facilitates access to the vulnerability that allows unauthenticated attackers to add fake administrator accounts to the dashboard.
“As this is an actively exploited zero-day vulnerability, and attackers are already aware of the mechanism required to exploit it, we are releasing this public service announcement (PSA) to all of our users,” reads Wordfence’s security advisory. “We are intentionally withholding certain details to prevent further exploitation. As a reminder, an attacker with administrator privileges has effectively achieved a complete site takeover.”
The vulnerability affects versions 3.5 and earlier of the plugin, and developers are yet to release a patch. Wordfence recommends that affected users remove the plugin completely until an official fix is released. Furthermore, the company rolled out a series of firewall rules for its Premium, Response and Care tiers and will do the same for Free tier users 30 days later.
Wordfence’s security advisory also included some indicators of compromise to help users determine whether their sites have fallen prey to the vulnerability. The most common clue is the presence of an administrator user account named rangex. Seeing the username in the dashboard means that the website has been compromised.
Another way to assess the website’s exposure to the attack is to check its access logs for requests to //wp-content/plugins/wpgateway/wpgateway-webservice-new.php?wp_new_credentials=1. Identifying the requests in the website’s logs is a solid indicator that it was targeted by an attack leveraging the WPGateway flaw, but it doesn’t necessarily mean it’s also been compromised.